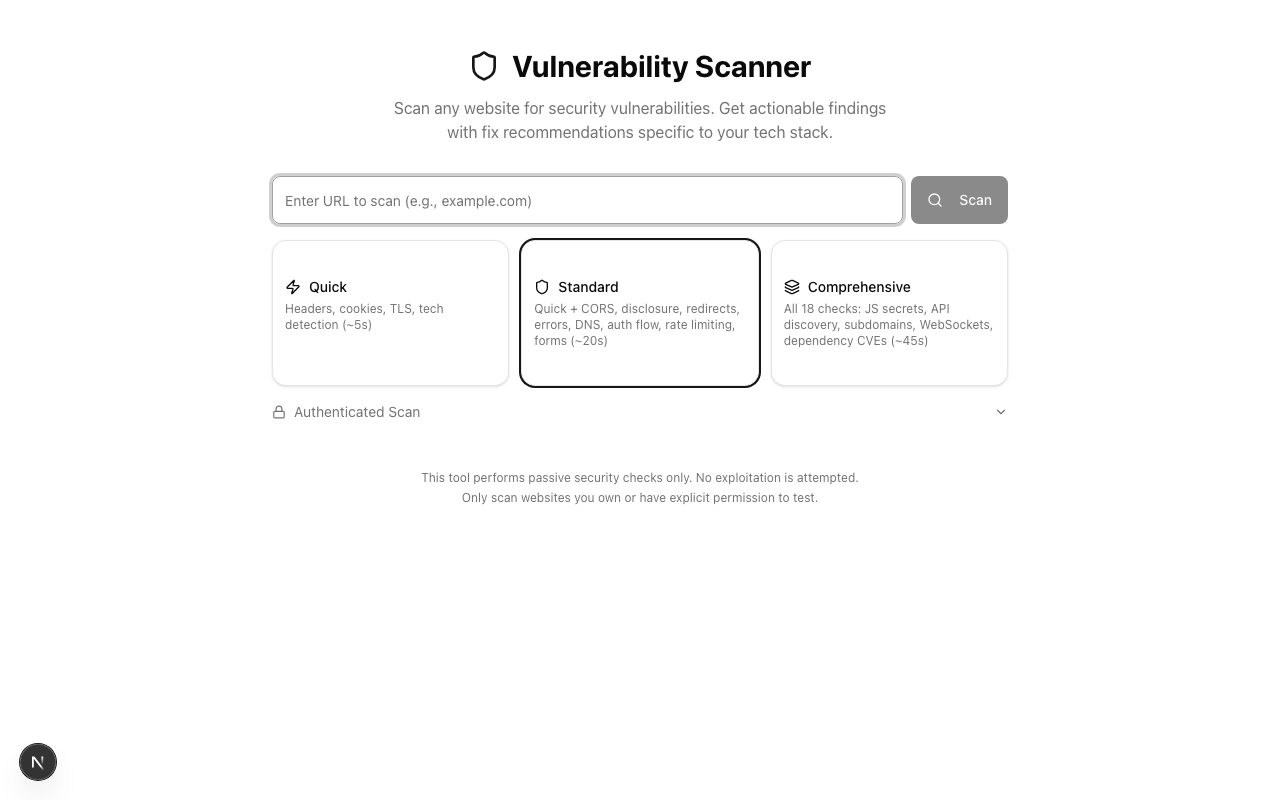
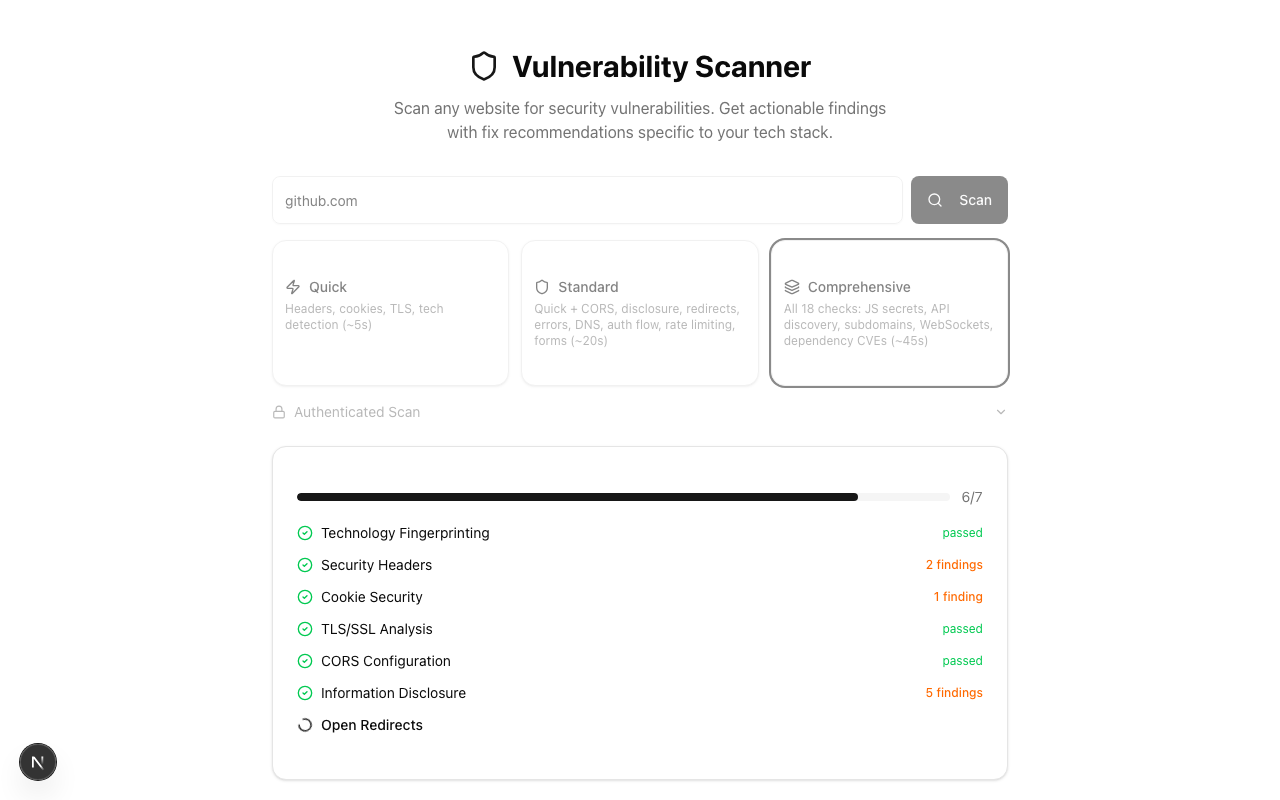
Enter a URL and choose scan depth
Paste any URL, pick between Quick (~5s), Standard (~20s), or Comprehensive (~45s) scan depth. Each tier adds more modules for deeper analysis.
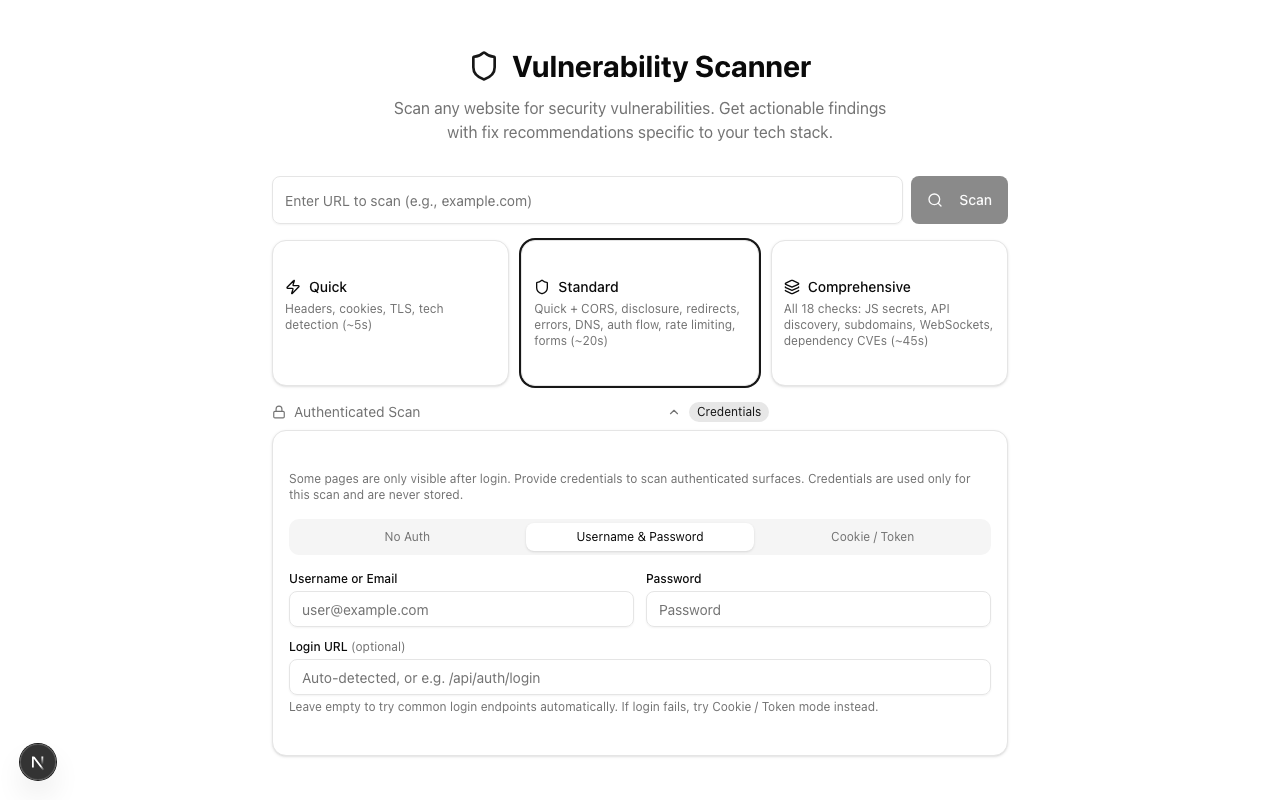
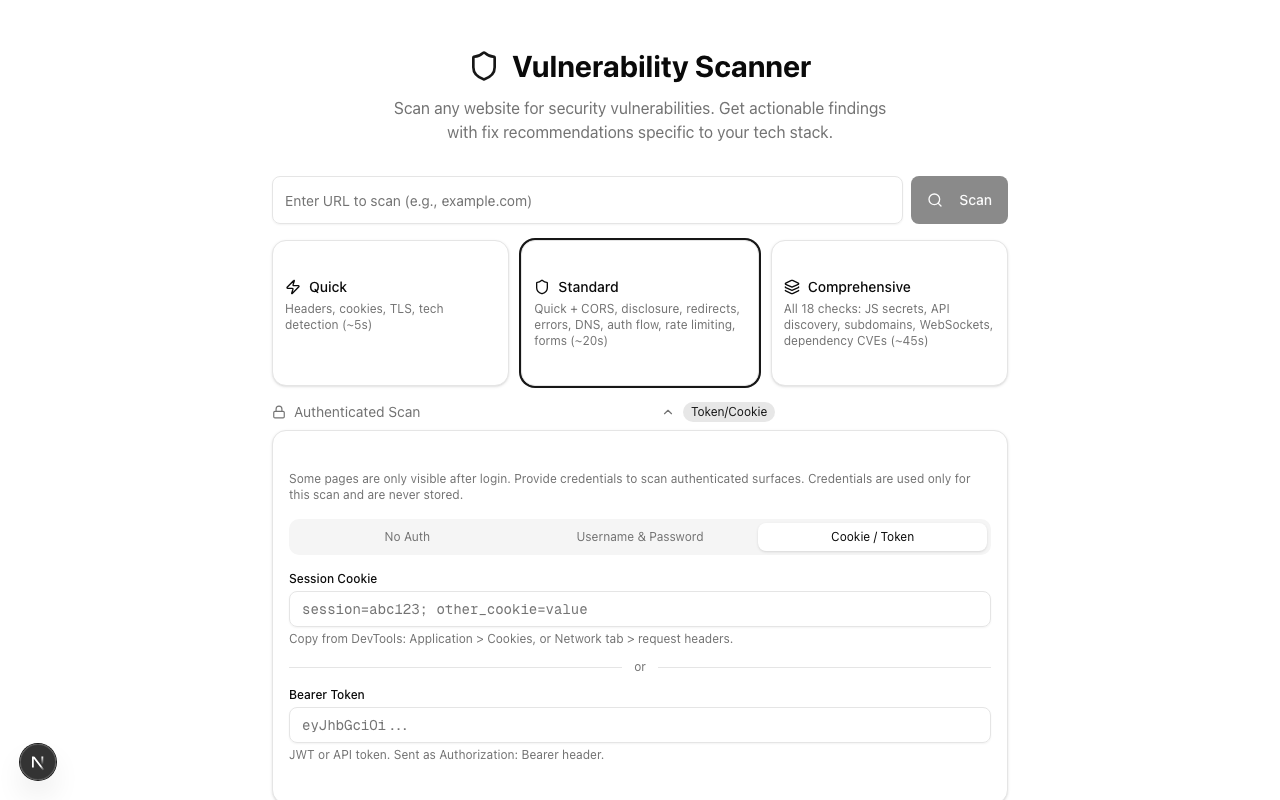
Scan pages behind login
Some vulnerabilities only appear on authenticated pages. Two modes let you scan behind login: enter credentials for auto-login, or paste a session cookie or bearer token directly.
Watch results stream in real time
The scan runs 18 modules in sequence, streaming results as each one completes via Server-Sent Events. You see exactly which modules passed, which found issues, and how many findings each produced.
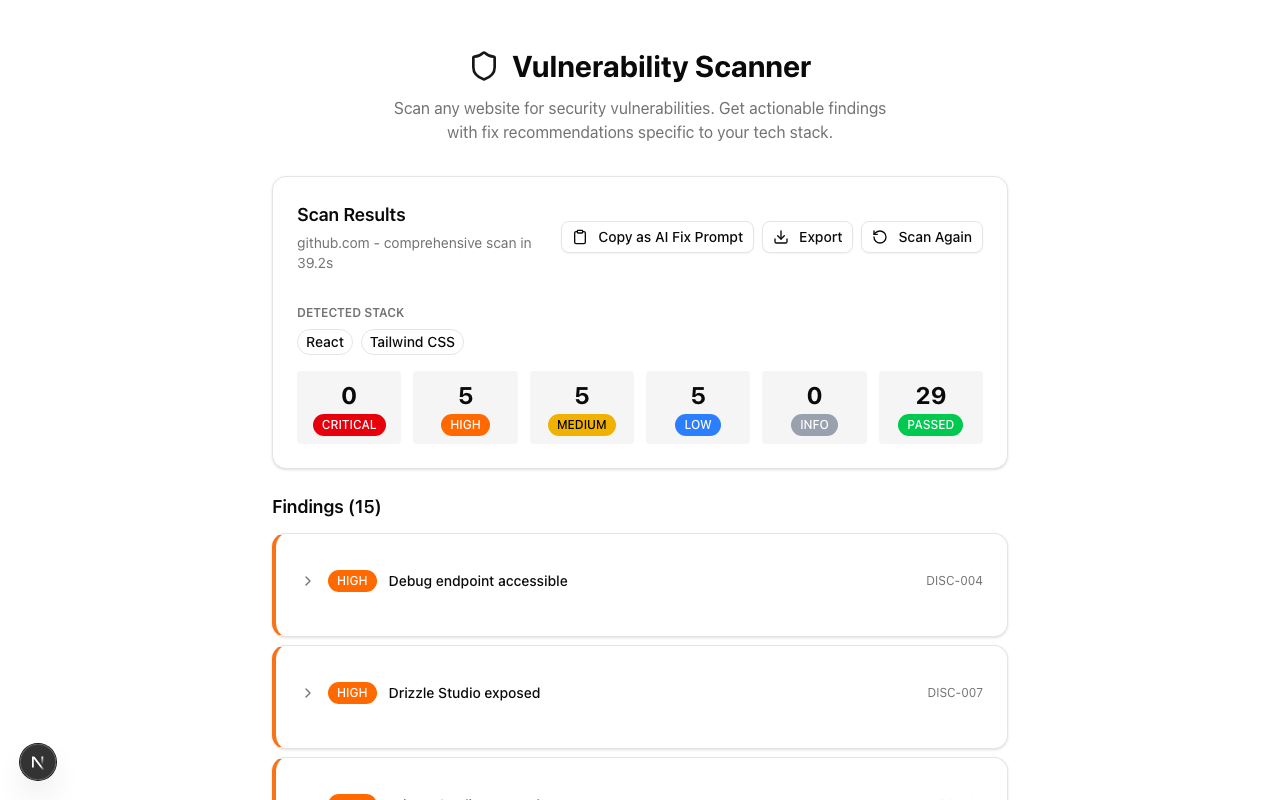
Clear severity breakdown at a glance
Results show a severity breakdown (Critical, High, Medium, Low, Info, Passed), detected technology stack, and action buttons for exporting or generating AI fix prompts.
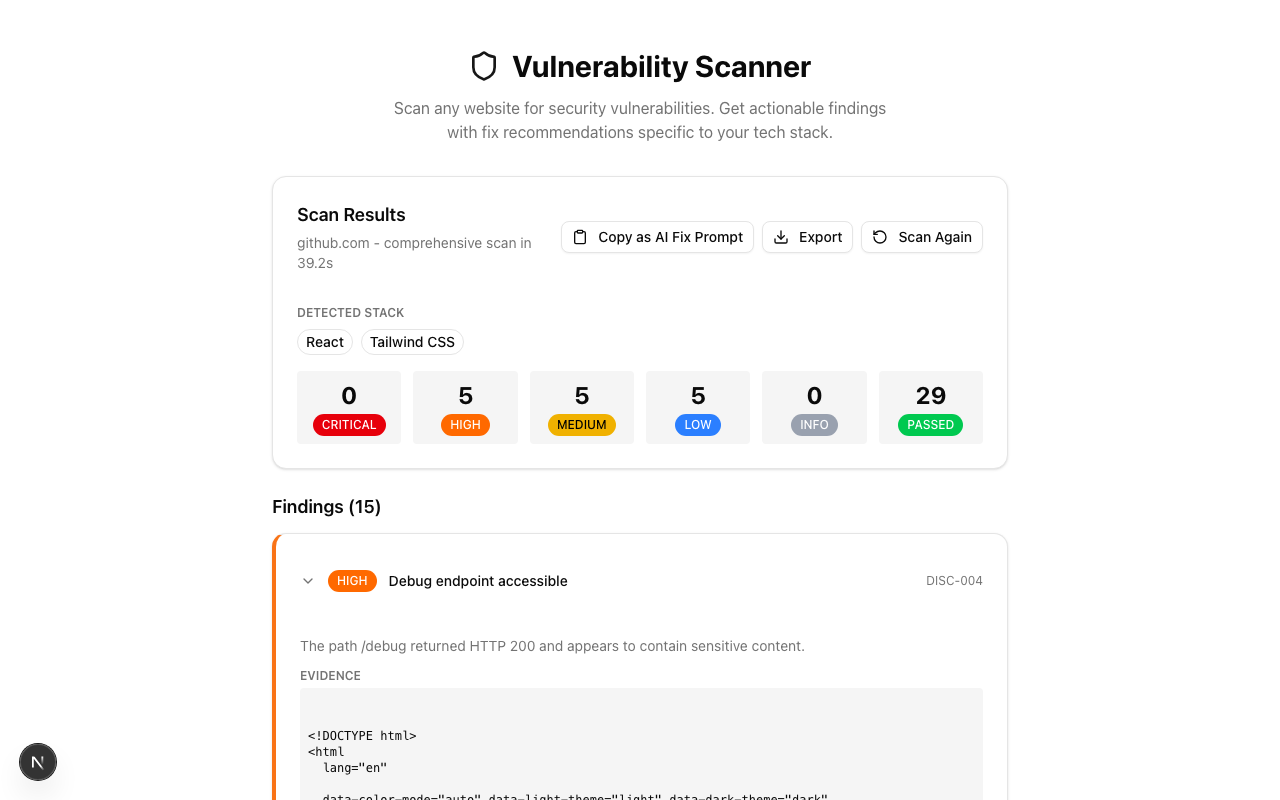
Detailed findings with evidence and fixes
Each finding expands to show a description, raw evidence, risk explanation, and a specific fix recommendation tailored to your detected tech stack.
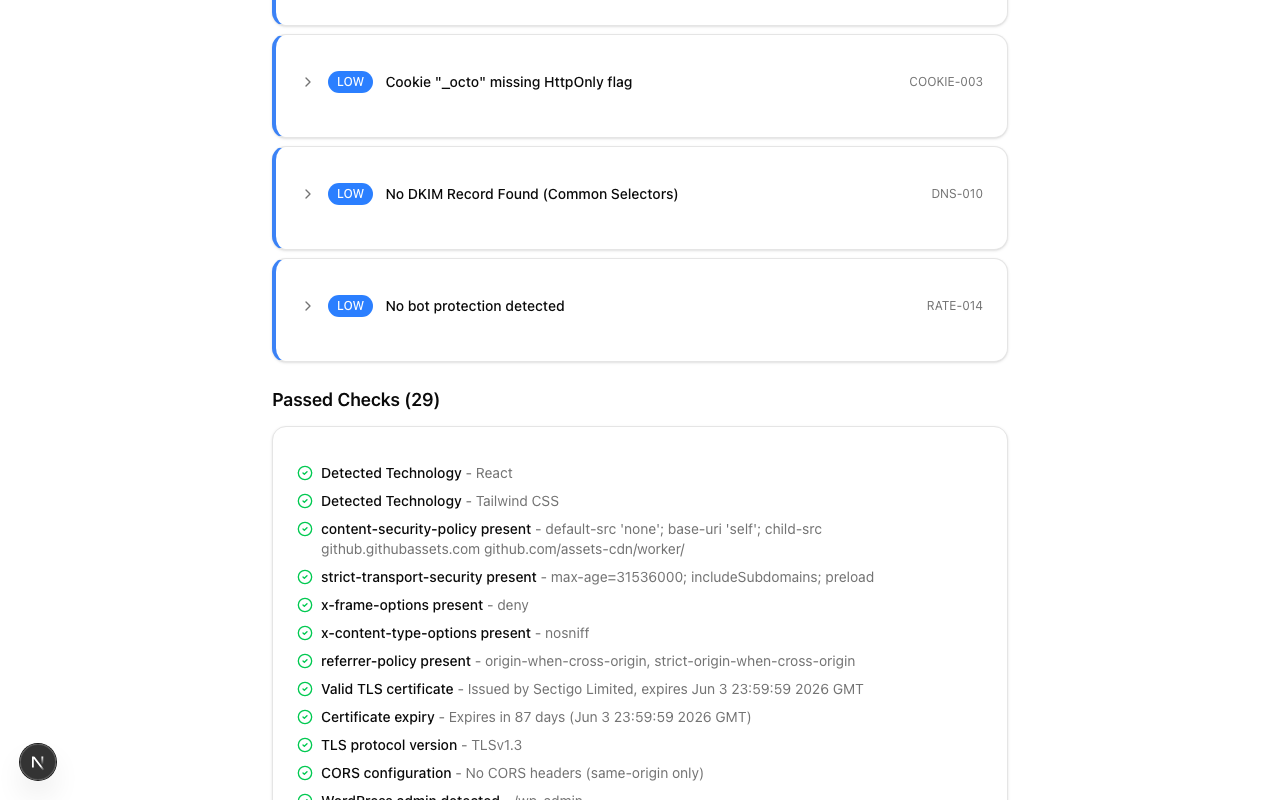
See what you're doing right
Passed checks aren't just a count — each one shows exactly what was validated. From Content-Security-Policy directives to TLS versions, DMARC records to form security.